6.1. Configuration
suSSHi Proxy is configured with the reachability information like hostname or IP address (and port if not default 22) together with a uniq proxy realm used by the connecting user to identify the secure cloud environment to connect to.
Suppose our protected environment is a customer tenant with a public cloud provider that uses private IP addresses within
the tenant and has few external IP addresses on the Internet.
The customer tenant is named after the project, let’s say ABC.
For this setup to work, we plan to deploy a suSSHi Proxy within the public cloud tenant and assign it an external IP
address that will allow access from our suSSHi Gateways located on-site in the company’s data center with Internet
accessibility.
The external IP address is given a DNS name, e.g. susshi-proxy.abc-cloud.company.com.
Let’s see what the steps are …
Navigate to Proxies > New and add the mandatory information for
Name,Realm,Hostname / IP AddressandPort.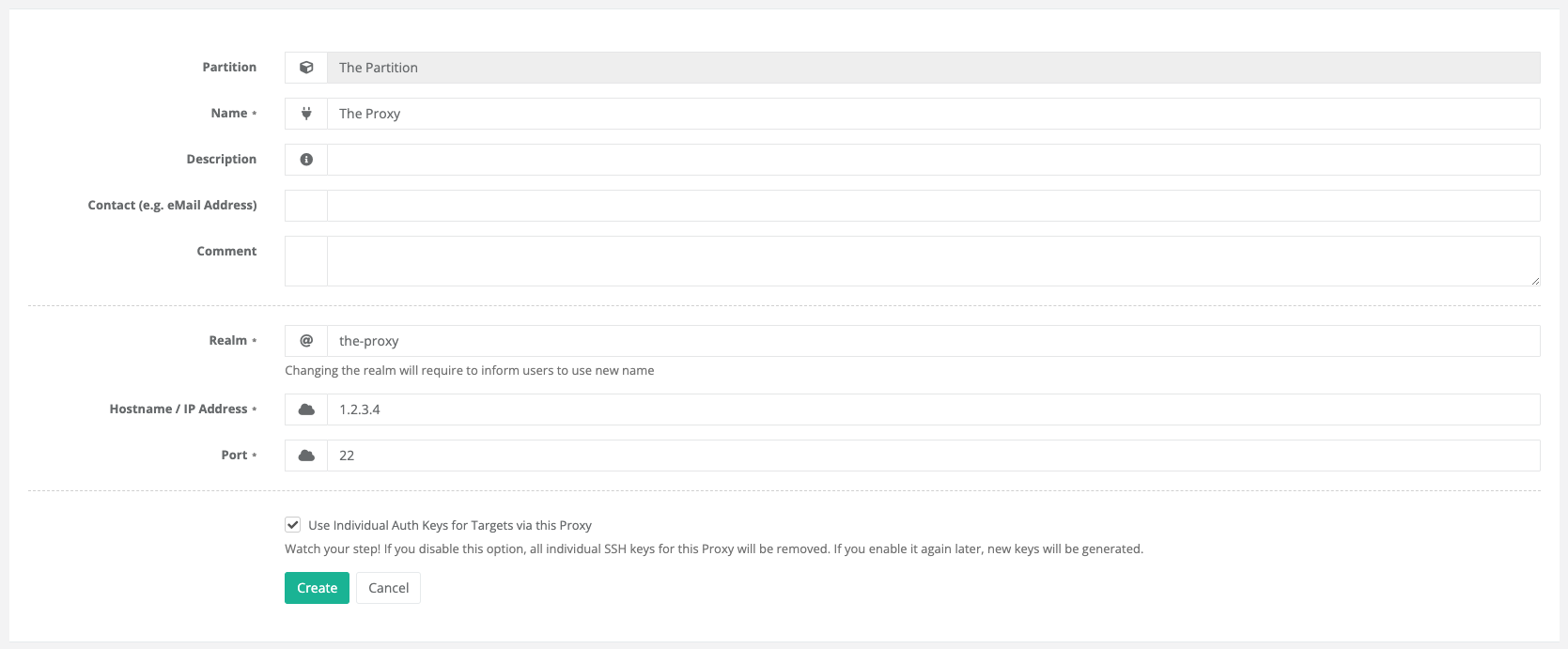
Afterwards, click
Create.Next, download the JSON configuration file for this new proxy. Press the
Downloadbutton in section Configuration > Option 1.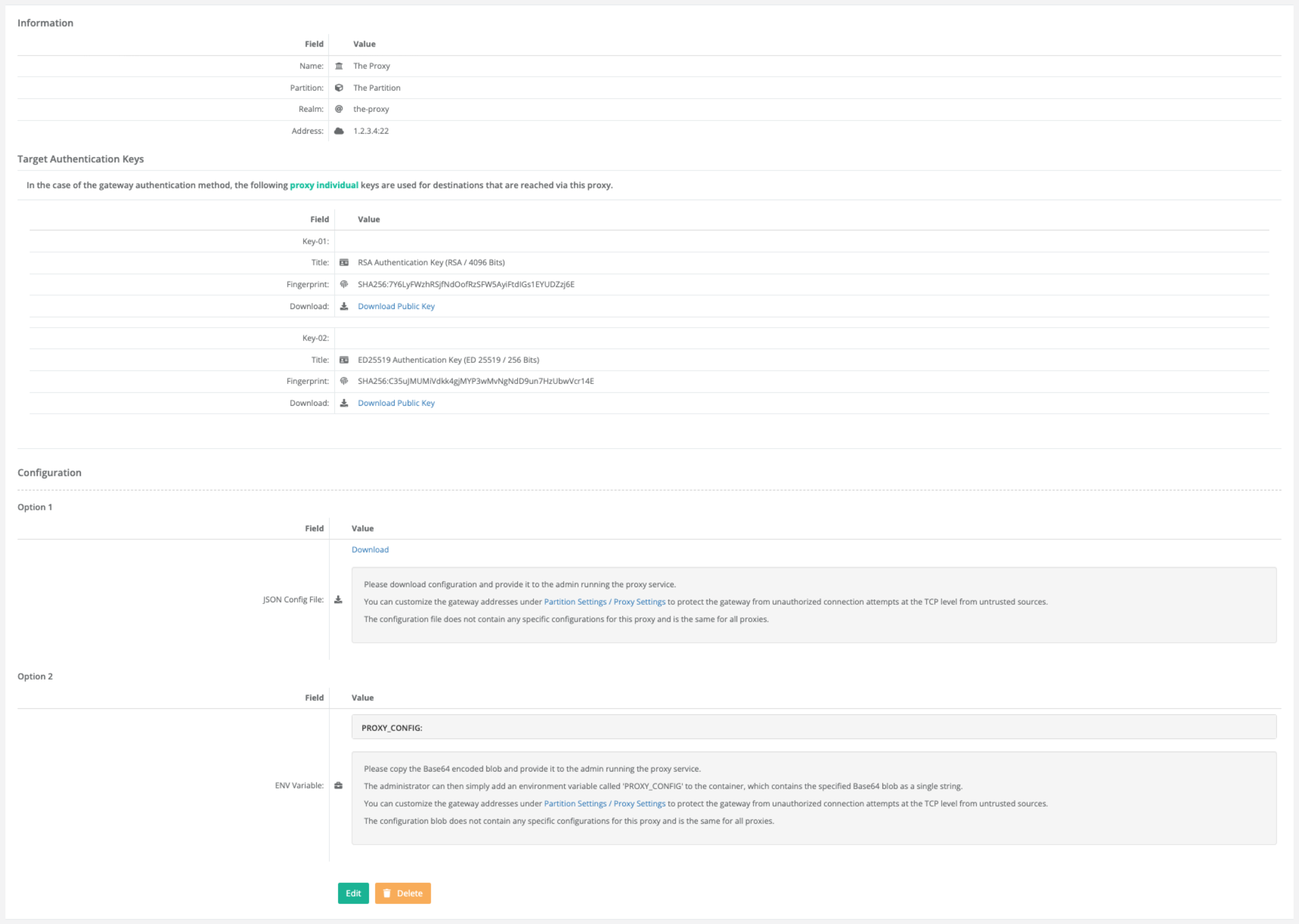
The configuration file contains all settings required to run the proxy instance you just configured. You may edit the file and change the gateway addresses to include only IP addresses or networks containing the company’s on-premise suSSHi Gateway IP addresses, which provides another level of protection for the suSSHi Proxy.
"GatewayAddresses": [
"0.0.0.0/0",
"::/0"
]
It is also recommended to configure a firewall in your cloud tenant to allow access only from the trusted Gateway IP addresses.
The configuration file looks the same for all suSSHi Proxies within the same partition and changes only if you change the gateway hostkeys or authentication keys. As long as those parameters are not changed, you can provide the same configuration file to all administrators who set up a suSSHi Proxy instance within the same federation.